What Is Technology Risk? How to Manage Business Threats
Introduction to Technology Risk
Almost every modern business utilizes technology in some capacity to enhance its product management and services. While eliminating manual methods mitigates some business risk in and of itself, it also introduces other threats.
Technology risk refers to the likelihood of software breakdown that can impair a company's system landscape. With proper assessment, organizations can mitigate these technology risks and optimize their business intelligence.
What is Technology Risk?

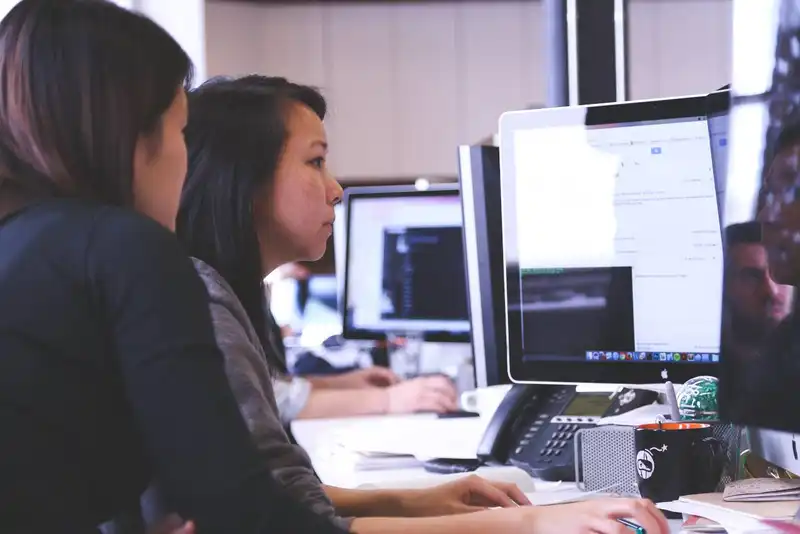
In the business realm, technology risk is the threat of management technology failure that could compromise cyber security and business intelligence. This cyber risk can come in many forms, including inefficiencies, theft, and malware. However, the primary threats revolve around software architecture, tooling, and delivery and maintenance.
These types of risks make technology risk management essential for modern businesses that utilize automated internal processes. Proactive technology risk management can identify and mitigate emerging threats before they have a chance to jeopardize business intelligence. This minimizes the snowballing effect where unnoticed, minor errors accumulate to irreconcilable damages.
Software Architecture
Depending on the solution, the software architecture may be outdated, creating unnecessary inefficiencies. Old infrastructure can silo data, disjoint departments, and restrict data sharing, making it impossible to compile data accurately.
When systems store information separately, they tend to differ in format and expose the business to inflated risks of theft. Unprocessed data makes it even more challenging to generate reports and diagnostics.
Tooling
Many legacy systems also use tooling, which establishes an extensive set of various features applicable to different departments. While a wide array of tools may seem appealing, it is also expensive and can make it challenging to train employees. Some tools may even require additional hardware to use, adding more operational expenses.
Delivery and Maintenance

Solutions that require extensive human intervention to implement increase the risk of human error and misconnections. This assumes extensive future maintenance, which can eat up much time, energy, and resources. As a result, businesses may have difficulty adapting to evolving technology.
Benefits of A Technology Risk Assessment
By regularly performing technology risk assessments, companies can minimize the impact of threats and reinforce software security. However, enterprise risk assessments also provide organizations with several other benefits.
Reduced Costs

Businesses that maintain a technology risk assessment schedule can avoid unnecessary costs to resolve technological issues. IT managers can also perform assessments before implementing a system to ensure it meets the company's current needs. Otherwise, companies could end up paying for multiple systems that duplicate some processes and neglect others.
Minimized Risks
Automated systems rely on the underlying technology that businesses must keep up to date to avoid weaknesses from forming in firewalls. Outdated software can also trigger additional problems if it connects with other existing systems. This can create a bottleneck, delaying sequential operations and elongating system downtime. With technology risk assessment, managers can promptly detect and eliminate risks.
Enhanced Agility

Many businesses fear that with automation, they lose their authority and control over internal systems. However, operational risk assessments increase businesses' agility and responsiveness to internal activities. In fact, automation gives owners the opportunity to standardize various tasks to streamline operations and workflow.
Steps to Technology Risk Assessment
Performing a technology risk assessment is comprehensive but requires time and attention to detail.
1. List Potential Applications
First, project managers need to outline every established internal system, including solution integrators and other underlying technology. Adequate IT departments should have an ongoing document that records each software at the point of implementation. By defining the new technology landscape, businesses can scrutinize each component during the assessment.
2. Assess the Software

Managers then need to evaluate the versions of software that each department uses. Some companies source technology from one primary service provider that has multiple versions of the same basic software. Using the same infrastructure, businesses can implement accounting, inventory management, and point-of-sale solutions. This ensures that all systems can integrate seamlessly and share data.
3. Evaluate the Servers and Data Centers
Next, managers need to assess their data servers and centers for capacity and limitations. Many providers recommend assigning technology stacks to each server to optimize the functionality of data centers. A technology stack, or data ecosystem, lists all established systems so developers can combine them under a single application. This makes it easy for IT managers to review and verify data in real-time.
4. Connect the Software and Applications
After locating all solutions, it is time to map out the flow of data throughout the company. By illustrating the technology landscape, developers can connect disjointed software and servers for efficient data exchange. This also enables managers to define dependencies, bottlenecks, and inefficiencies.
5. Determine the Software's Impact
Lastly, companies need to define the probability and potential impact that risks have on their infrastructure. For example, if companies are unable to link their existing systems, they risk missing data that fall between sectors. Other organizations may be at risk of data deterioration unless they update their software.






